Did you know that May 7th is World Password Day?
Passwords are a necessity for any website that offers a private area for users and administrators. With WordPress’s content management system(CMS) providing an administrative dashboard, website owners are tasked with determining the right password requirements and implementing them in the application. The problem is implementing strict password requirements without making the application too difficult to work with for users. Users will leave a site if password requirements are too difficult, but they are a necessity to protect private areas of the website. Here are some tips when designing your user password standards.
Complex Passwords and Length
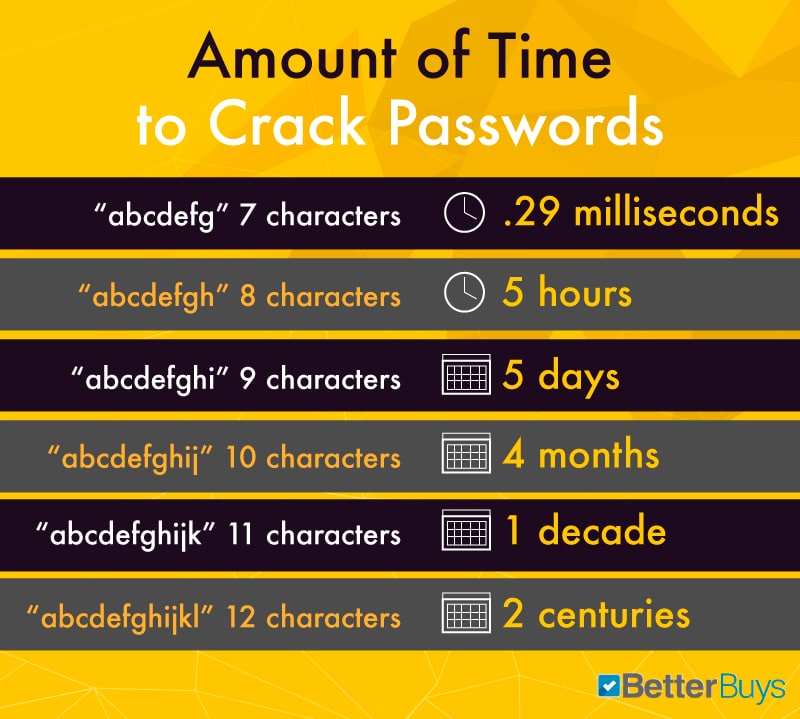
Size really does matter. It used to be that you could just require long passwords of at least 6 characters to form a legitimately good password. Unfortunately, as computer systems matured, cracking these passwords is easy with the right tools. And as computer processors get faster the length of time to crack gets shorter. Your user passwords should be at least 10-12 characters with at least one uppercase letter, at least one number, and a special character. These requirements increase the complexity of a password. Complex passwords can take years for a password cracker to determine values, so they are much more secure than simple, all lowercase passwords.
Other Password Tips
- Don’t use the same password for all accounts
- Don’t use common passwords like ‘123456’, ‘letmein’, or ‘password’. Our friends over at Safety Detectives did a deep dive into The 20 Most Hacked Passwords in the World – hop over and check if your is there.
- Don’t use Pwned Passwords – passwords that have been previously exposed in data breaches
- Don’t use the default ‘admin’ username
- Don’t share your WordPress login – set each user up with their own login credentials
- DO USE a password manager such as LastPass or 1Password – these allow for easy use of strong, complex, and unique passwords for all your logins
Implement Account Lockouts after Several Login Attempts
Brute force attacks are common with hackers when they know that they can continually “guess” a password by submitting login credentials to the site without any lockout periods. A lockout occurs when too many attempts were made to log into the user’s account. Each site has its own standards. Allowing five login attempts is standard. You might allow fewer login attempts depending on the sensitivity of the information inside the password-protected area.
The WordPress iThemes Security Pro plugin offers numerous password protection features such as:
- Require/enforce strong passwords
- Setting password expiration timelines
- Magic Link passwordless logins
- Two-Factor Authentication
- Brute force protection
- And so much more. . .
Force Password Resets after Suspicious Activity
Even with password requirements in place, hackers will still test your site for good security. They might even phish passwords from your internal employees. If they are able to gain access to the site through phishing, you have a security breach. Suspicious activity should always be logged through the application or using a third-party tool. For instance, if your company is located in Canada and you suddenly have an employee logging in from China, it is suspicious. You lock the account and reset the user’s password.
Always Use HTTPS
Any web page that requires users to input a username and password should use HTTPS. Pages using HTTP (unencrypted) traffic allow attackers to “sniff” network traffic and view the data contained within communication packets. If the user sends you a username and password to log into a section of the site, these credentials can be “sniffed” out and read if they are using HTTP. HTTPS is especially important for pages that require users to send sensitive data such as credit card numbers. Any payment page should always require HTTPS.
To avoid the email phishing issue, always have software on the email server that filters out suspicious email events such as those containing executable attachments.
Validate SQL Input
For each password page, you should always validate your SQL statements if you don’t use stored procedures. SQL injection attacks are successful when an attacker is able to send malformed SQL statements and run them on the database server. They can then dump the table that contains usernames and passwords of your users. Never run dynamic SQL statements on the server without first validating that they are properly formatted.
These five tips will help you provide better security for your website applications. It isn’t a complete list, but it will get you started as you build password-protected sections on your site.





